Anti-Phishing, DMARC , Cyberwarfare / Nation-State Attacks , Email Threat Protection
Google Suspends YouTube Accounts, Content Linked to Iran
'State-Sponsored' Phishing Activity Alert Follows Facebook and Twitter Warnings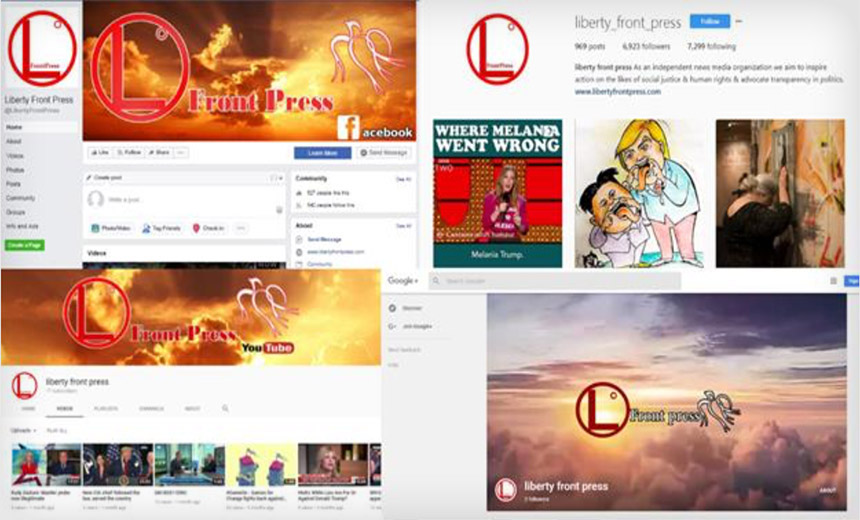
Technology giants continue to ramp up their efforts to identify, block and expose accounts and online activity that they have tied to government-run operations designed to influence electorates or wage information warfare (see Facebook, Twitter and Google Suspend 'Inauthentic' Accounts).
On Thursday, Alphabet's Google said it had alerted a number of its users on Monday that they appeared to have been targeted or come into contact with phishing attacks being run by the Iranian government.
Google also announced that it had suspended 39 YouTube channels that collectively logged 13,466 total U.S. views of relevant videos, six blogs on Blogger and 13 Google+ accounts that contained political content as part of an apparent influence operation. It says all had disguised connections to the state-run Islamic Republic of Iran Broadcasting media outlets.
"Our investigations on these topics are ongoing and we will continue to share our findings with law enforcement and other relevant government entities in the U.S. and elsewhere, as well as with others in the industry," Kent Walker, Google's senior vice president for global affairs, says in a Thursday blog post.
Google's moves occurred concurrently with Facebook and Twitter also suspending a number of "inauthentic" accounts that they tied to separate, apparently Iranian and Russian government operations.

Facebook on Monday said it had removed 652 pages, groups and accounts tied to two separate government-run campaigns - one tied to Iran, the other to Russia.
Twitter, meanwhile, said that it "suspended 284 accounts from Twitter for engaging in coordinated manipulation."
Nexus: Liberty Front Press
The Iranian-run efforts all appeared to be tied to a group called "Liberty Front Press," cybersecurity firm FireEye says in a Monday blog post. On Thursday, FireEye also released a more in-depth report analyzing the "suspected Iranian influence operation."
It says with "moderate confidence" that the various Liberty Front Press efforts appear to have been run by Iran's state media. But it says the clues it has used to make that assessment could have been planted by someone else.
Promotional and Registration Connections Between Suspect Iranian Inauthentic Sites and Social Media
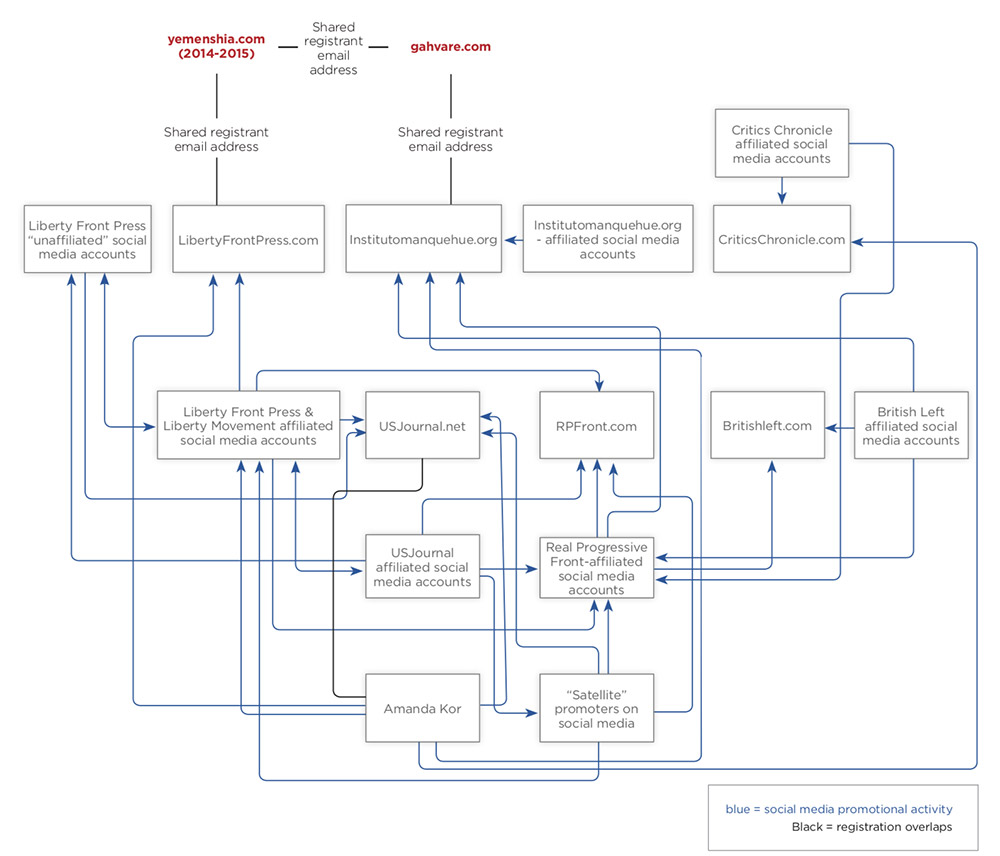
Liberty Front Press used a number of pages disguised to look as if they had originated with various groups or individuals. Pages and social media accounts that Facebook and FireEye say the group ran featured names such as:
- Pray For America
- Free Scotland 2014
- The Agitators
- The British Left
- Patriotic Palestinian Front
- Manquehue Institute
- Real Progressive Front
- Critics Chronicle
- Berniecratss
- U.S. Journal
Facebook and Google explicitly thanked FireEye for sharing intelligence that helped guide their efforts to suspend accounts and remove content.
Google Issued First Iranian Hacking Alert in 2011
Google says its internal teams continue to track threat actors, but it's also a customer of FireEye's threat intelligence service. "We're grateful to FireEye for identifying some suspicious Google accounts - three email accounts, three YouTube channels and three Google+ accounts - which we swiftly disabled," Walker said.
Walker notes that Google has been tracking campaigns being run by the Iranian government, and says it first warned its users - in that case, about a man-in-the-middle attack - in 2011. He notes that the Liberty Front Press efforts that led to the Monday takedown of various types of content appear to have begun in January 2017, and that Google has identified "a broader range of suspicious actors linked to Iran who have engaged in this effort" than FireEye alone detailed.
"Actors engaged in this type of influence operation violate our policies, and we swiftly remove such content from our services and terminate these actors' accounts," Walker said. "Additionally, we use a number of robust methods, including IP blocking, to prevent individuals or entities in Iran from opening advertising accounts."
For users, meanwhile, he repeated Google's recommendation that anyone at risk from such attacks - especially "political campaigns, journalists, activists and academics" - use two-factor authentication to protect themselves (see Nation-State Spear Phishing Attacks Remain Alive and Well).
Other technology firms say they also continue to track and block such efforts (see Facebook Reveals Ongoing Political Influence Campaigns).
Nation States' Social Media Manipulation
U.S. intelligence officials have said that while numerous countries have capabilities to run online campaigns, Russia, China, Iran and North Korea pose the greatest risk.
Google likewise noted that "the state-sponsored phishing attacks, and the actors associated with the IRIB" that it called out on Monday "are clearly not the only state-sponsored actors at work on the internet."
The Russian troll farm known as the Internet Research Agency, which was indicted earlier this year together with 13 Russian national employees for information warfare activities against the U.S. used Facebook, Twitter and Google properties as part of their efforts (see Putin Offers Extradition Promise to US: 'Never').
Following that indictment, "we have continued to monitor our systems, and broadened the range of IRA-related actors against whom we've taken action" Google's Walker says. "Specifically, we've detected and removed 42 YouTube channels, which had 58 English-language political videos - these videos had a total of fewer than 1,800 U.S. views. We've also identified and terminated the account associated with one blog on [Google's] Blogger."
Iran's Longstanding Online Operations
Clint Watts, a research fellow with the Foreign Policy Research Institute, tells the Wall Street Journal that Iran has run influence operations for years. But he says they've received less attention than Russian efforts because Iran doesn't appear to have been trying to influence U.S. elections.
In March, the U.S. Justice Department unsealed an indictment accusing nine Iranian nationals of being part of a five-year hacking campaign designed to steal scientific research from other countries. Prosecutors accused the group of stealing more than 31 terabytes of data from 320 universities in 22 countries - including 144 U.S. institutions - as well as multiple businesses and government agencies (see Britain Backs US Hacking Allegations Against Iranians).
In June, Robert Hannigan, former head of the U.K.'s Government Communications Headquarters signals intelligence agency, said it was likely that Iran would ratchet up its online attacks against the U.S. in reprisal for the Trump administration in May announcing that it was withdrawing from the Iran nuclear deal (see Cybercrime Groups and Nation-State Attackers Blur Together).