Sponsored by BeyondTrust
Privileged Access Management (PAM) Buyer’s Guide and Checklist
Sponsored by LastPass
Integrating IAM Infrastructure Financial Sector vs Media & Tech
Sponsored by CyberArk
Securing The Enterprise's Cloud Assets on Amazon Web Services (AWS)
Sponsored by CyberArk
Securing Privileged Access and Identities in 4 Key Cloud Scenarios
Sponsored by LastPass
Identity and Access Management: Industry Driven View
Sponsored by BioCatch
Gartner: Market Guide for Identity Proofing and Affirmation
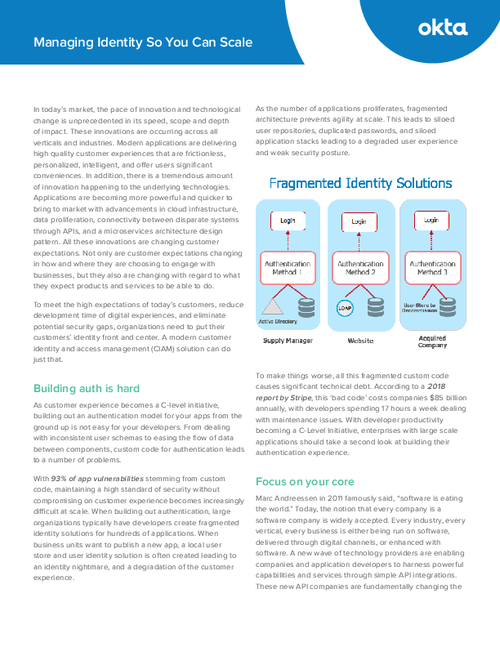
Sponsored by Okta
Managing Identity So You Can Scale
Sponsored by Okta
Identity as a Service for Dummies
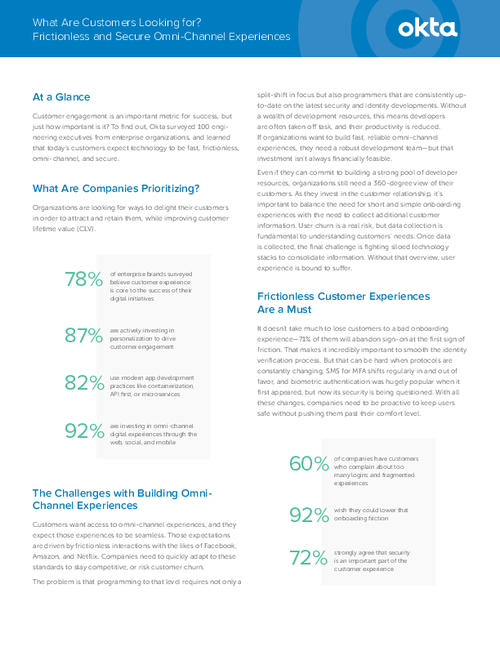
Sponsored by Okta
5 Arguments to Justify Your Identity Spend
Sponsored by Okta
Zero Trust: A Global Perspective
Sponsored by Ubisecure
The Value of CIAM Investments: Save Costs & Increase ROI
Sponsored by Ubisecure
Build vs. Buy: Identity & Access Management
Sponsored by LastPass